Financial scams and malware-assisted remote access attacks are on the rise, as industrial-scale fraud operations continue to proliferate in Southeast Asia. Many countries in the region have issued official warnings over the past three years. However, tracing specific malware strains back to these notorious complexes remains a difficult challenge to this day.
In collaboration with the Intel Threat expert team. Infoblox – a cybersecurity company based in California, USA, Anti-Phishing has conduct an investigation An Android trojan was operating from multiple locations, including the K99 Triumph City complex in Cambodia. This conclusion was reached based on technical analysis, testimony from escapees, and evidence obtained from within the complex by the victims of human trafficking themselves.
This complex has been widely recognized by the United Nations and numerous other organizations as a fraud hub with links to high-ranking, powerful politicians, and using forced labor to operate large-scale malicious text messaging, calling, and email campaigns.
The premise of the investigation
Malware-as-a-Service platform detected.
A sudden surge in DNS queries from customers' cloud environments led Infoblox experts to discover a type of malware. Through analysis, the experts identified it as a platform. Malware-as-a-Service (MaaS) Sophisticated. This platform has the capability to:
- Real-time monitoring of all activity on the victim's device.
- Stealing login credentials and biometric data (fingerprints, facial recognition)
- Block SMS messages and calls
- Remote access to cameras and microphones.
- Installing additional malware after infiltrating the device.
- Control all devices remotely using professional monitoring software.
Experts have also discovered hundreds of domain names used to attack victims, many of which were cleverly designed to impersonate government agencies. These DNS anomalies were first noted a year ago, but traces of this Trojan may date back to at least 2023.
An estimated 35 new domain names are registered each month. Among the customers using the solution... Infoblox Threat Defense Cloud, The areas most severely affected were Southeast Asia, Europe, and Latin America. The highest number of inquiries were recorded from clients in Indonesia, Thailand, Spain, and Turkey, indicating the global reach and impact of this group of actors.
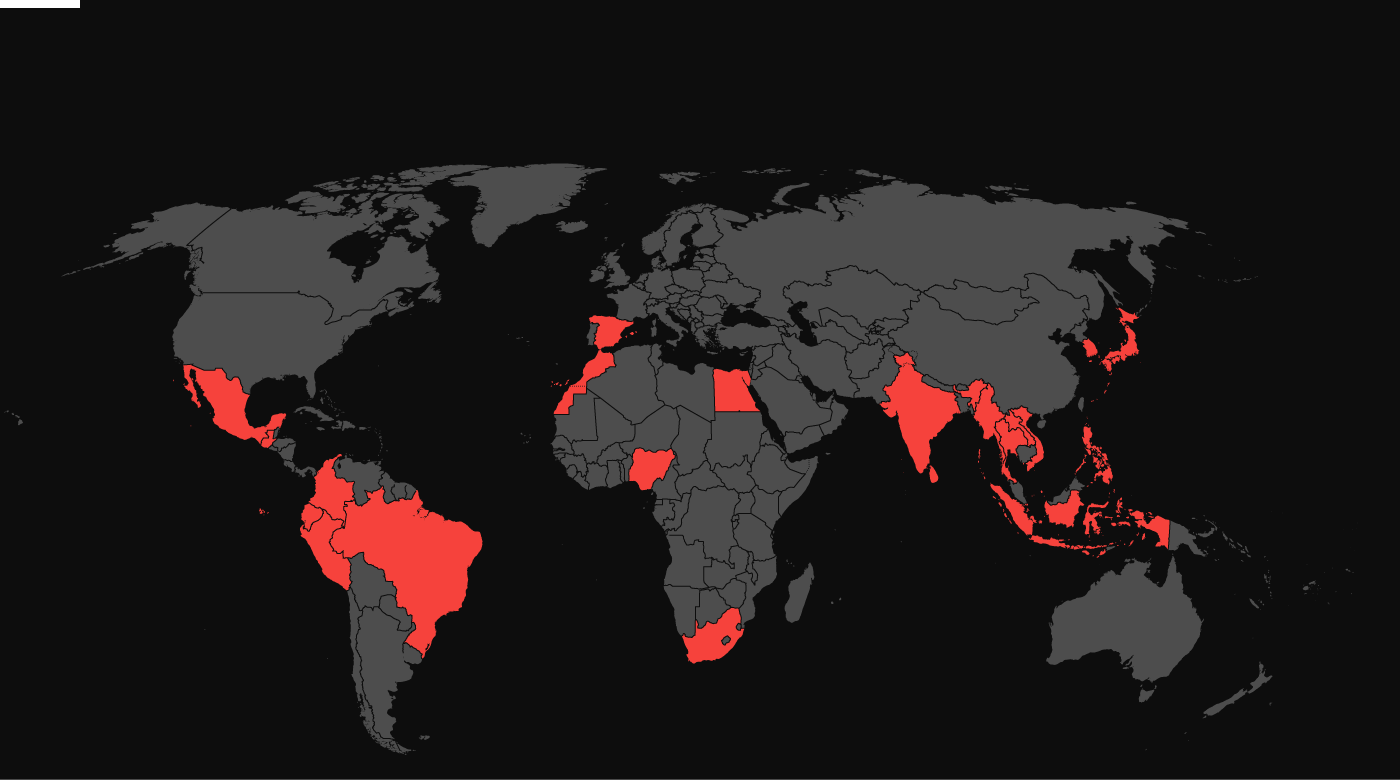
Further investigation revealed overlaps in infrastructure and behavior between this MaaS platform and the past activities of identified threat actors. Vigorish Viper and Vault Viper. These connections reveal a large-scale, multilingual phishing campaign targeting victims in at least 21 countries across 4 continents (as shown in Figure 1).
Based on linguistic cues, infrastructure patterns, and operational characteristics, experts assess that this malware is highly likely to belong to an unidentified Chinese-speaking MaaS administrator. This individual is currently providing services to numerous phishing operations in the Greater Mekong Subregion, which is used as a base for distributing malware and carrying out online scams. There have been numerous reports of forced labor in this region.
Evidence from inside the fraudulent complex.
From a number of victims who were held captive and forced to commit fraudulent acts inside the complex. K99 Triumph City, Anti-Phishing The necessary evidence was gathered to establish a link to this specific Trojan family. Key details about the scams' internal workings, provided by the evaders, along with malware analysis from Anti-Phishing, paved the way for the investigation team to delve deeper and monitor their activities in real time.
Experts witnessed firsthand the alarming extent of this trojan's intrusion: it gave attackers complete control over infected devices, allowing them to monitor victims and steal data directly. Furthermore, the investigative team found evidence of fragmented C2 (Command and Control) dashboards categorized by target country (e.g., “Indonesia Group,” “Brazil Group,” “Egypt Group”), and in some cases, by the names of specific “clients.” This suggests a well-organized hierarchical structure with tight coordination and management.
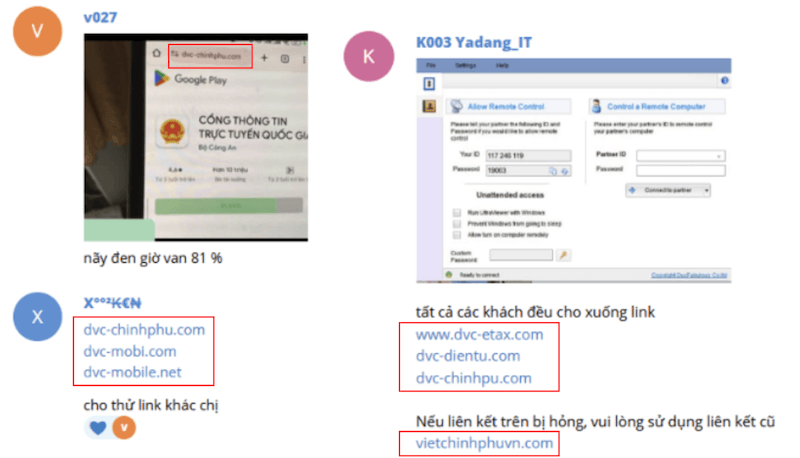
This report includes details of the scam campaign, gathered directly from individuals who were held captive at the K99 complex and forced to participate in cybercrime activities. In addition to witness accounts, escapees provided screenshots as direct evidence reinforcing the link between the domains Infoblox was monitoring and activity at the complex.
The origin and model of DNS
Abnormal DNS query
In March 2025, experts from Infoblox observed a surge in customer queries (Figure 2), along with a sharp increase in domain name registrations. Data showed that the majority of affected customers were from Southeast Asia, Europe, and Latin America; with the highest query traffic coming from Indonesia, Thailand, Spain, and Turkey. These unusual signs prompted them to investigate, ultimately leading to the discovery of an Android banking Trojan.
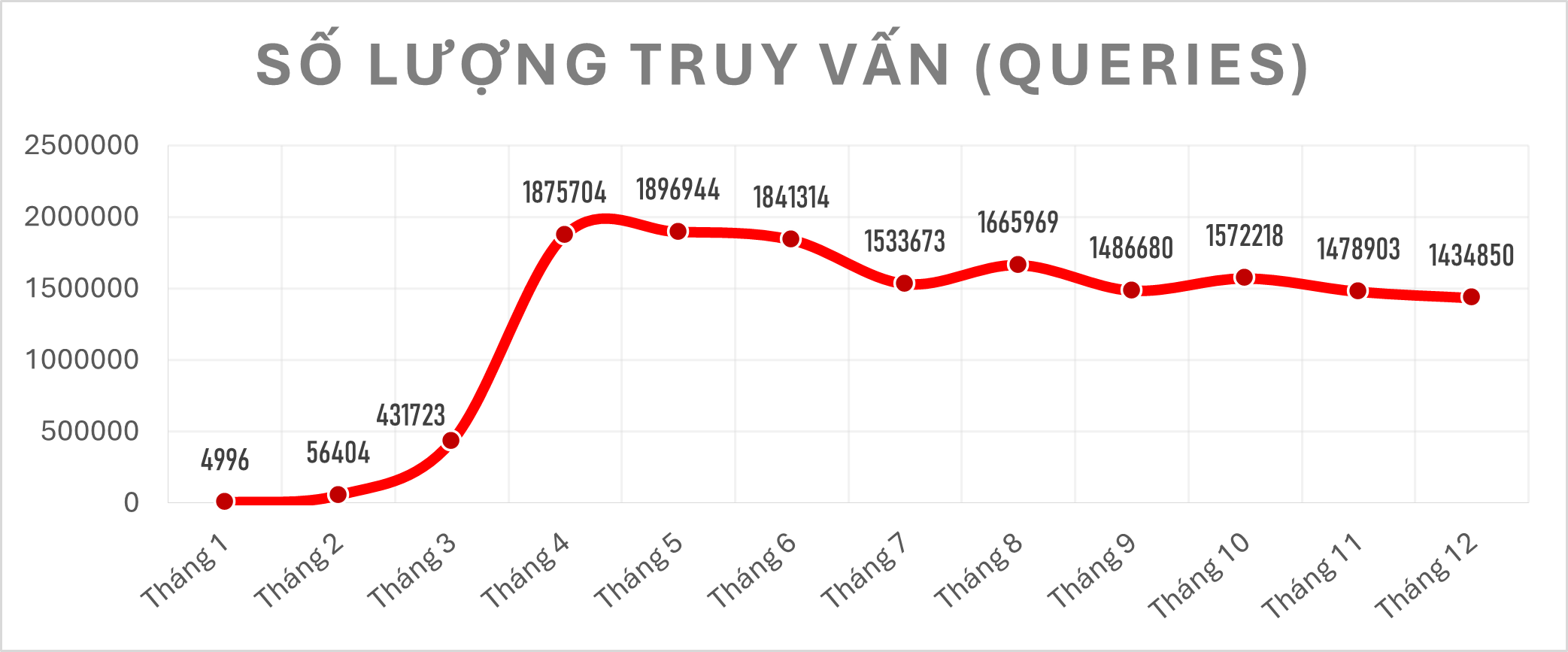
This campaign is still very active, with approximately 35 new domains registered each month. Attackers use both domains generated by the Registered Domain Generation Algorithm (RDGA) and lookalike domains – which are designed to impersonate legitimate organizations and public services in order to spread malware.
These domain names are cleverly designed to impersonate banks, pension funds, social security organizations, utility providers (electricity, water), as well as tax, immigration, telecommunications, and law enforcement agencies. The table below provides some examples.
| Domain name | False target (Country/Organization) |
|---|---|
| vsgo[.]cc | Philippine Social Security System |
| nmxgo[.]cc | South African police |
| orgo[.]cc | Indonesian State Pension Fund |
| idphil[.]net | Philippine Department of Information and Communications |
| immigration-kr[.]net | Korean Immigration Office |
| openbank-es[.]com | Openbank Spain |
| googleplay[.]djppajakgoid[.]com | Indonesian Tax Directorate |
| cedula-registraduria-gov[.]org | National Civil Registry of Colombia |
Infrastructure analysis and acquisition methods
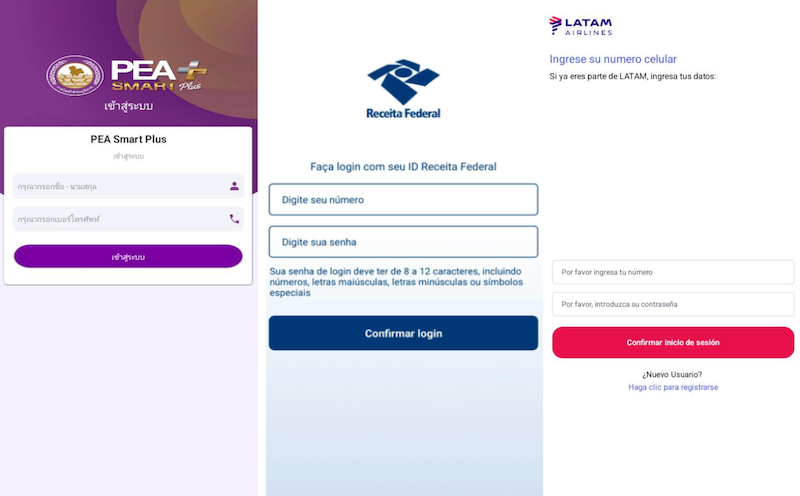
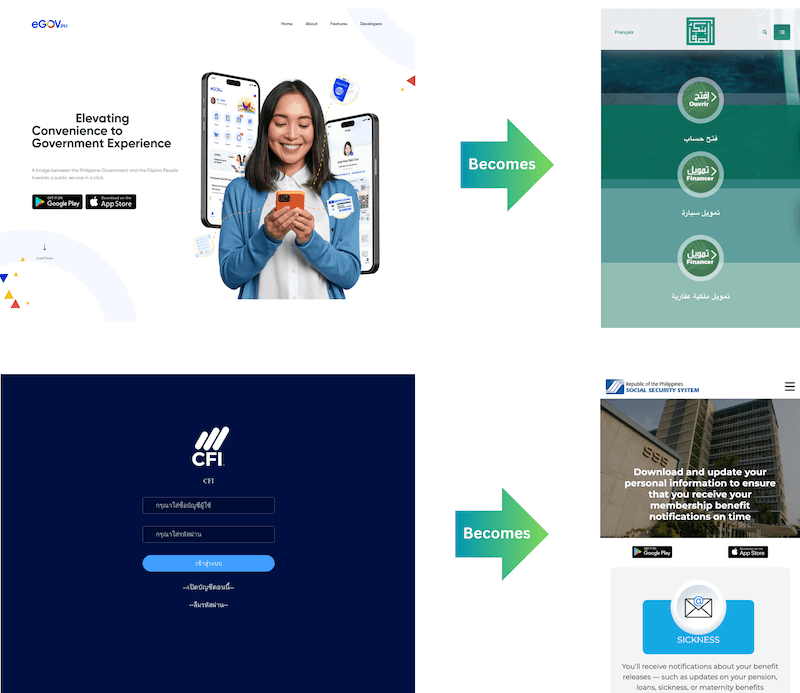
Figure 3 below shows some examples of the bait pages used. Recently, the scope of this phishing campaign has expanded both geographically and geographically, including bait pages targeting airlines and e-commerce platforms, as well as extending to countries in Africa and Latin America.

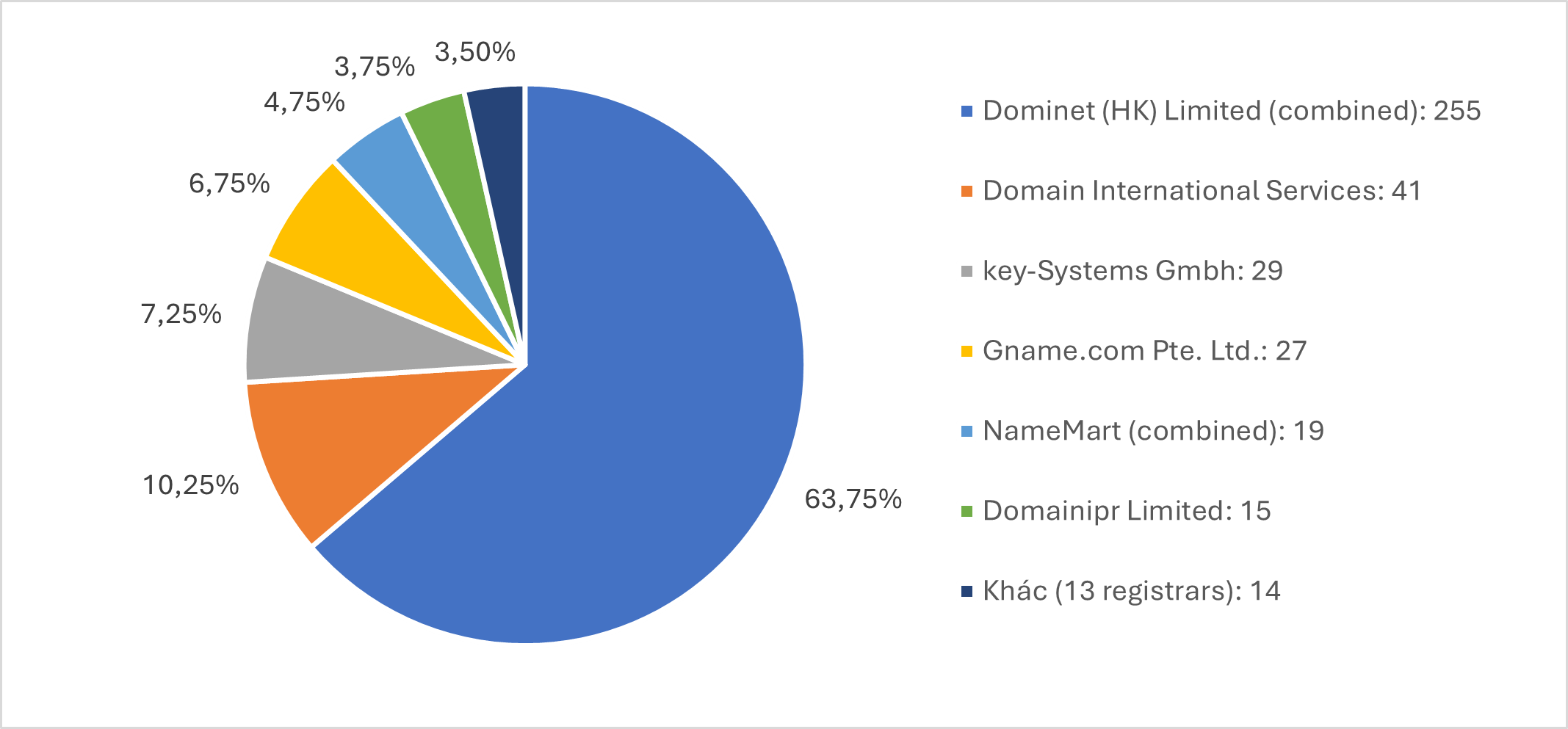
Experts analyzed 400 decoy domains registered in 2025 used for phishing and malware infection. Evidence suggests these domains were part of a coordinated and centrally managed campaign, designed to be scalable and resilient (against sweeps).
Domain name registration for bait sites is primarily concentrated at Hong Kong-based registrars such as Dominet (64%), Domain International Services (10%), and Namemart (formerly Domain International Services – 7%), accounting for 81% of identified infrastructure (Figure 4). This group of actors particularly prioritizes top-level domains (TLDs) such as .com, .top, and .cc, accounting for approximately 861 TP3T of the total number of domain names. Most of these domain names are hidden behind Cloudflare's service.
There is a clear strategy in domain name creation: use a 2- to 5-character prefix, followed by a carefully chosen suffix (usually '‘go’' or '‘gov’This is most likely intended to mimic legitimate government top-level domains such as ). .go and .gov, supporting social engineering and impersonation of government agencies. In some cases, domain names also include geographically specific suffixes such as '‘ph’, ‘th’' and ‘vn’ (Vietnam), as well as longer suffixes such as '‘ind’, ‘mxco’, ‘Peru’' and '‘Africa’.
The domain names used for the C2 control system and other administration panels have slightly different naming conventions and utilize TLDs such as .top, .xyz, .vip, and .pro. However, there is a clear preference for the tail. .top (This accounts for 39 out of the 42 active C2 domains). All C2 domains use the registrar Domain International Services, Namemart, and the name servers of DomainNameDNS.
chain of attacks
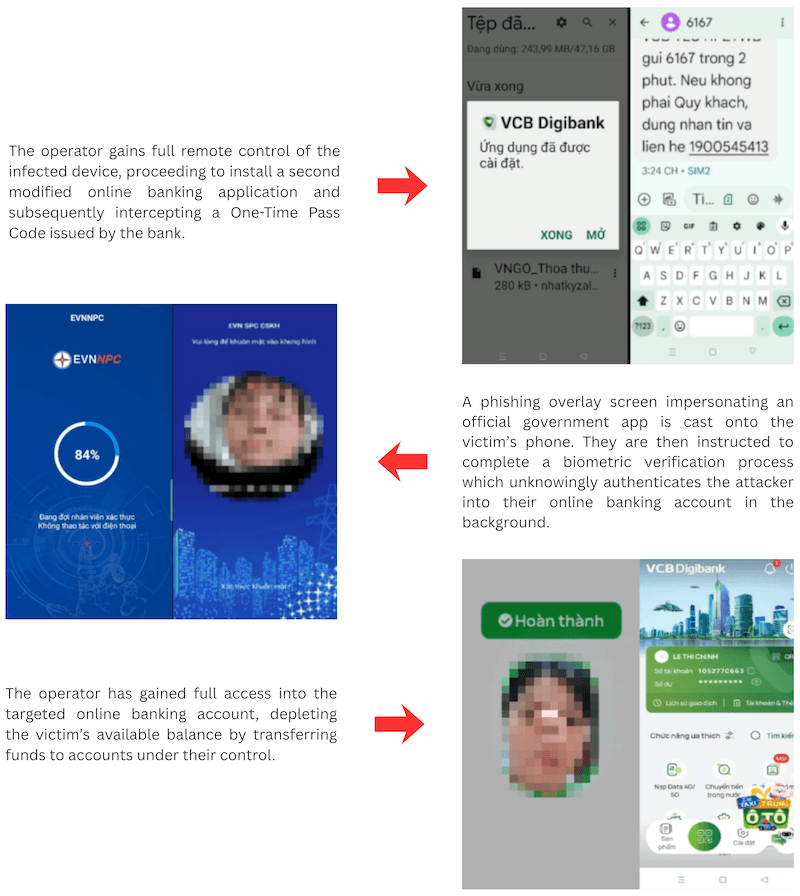
The attack involves multiple stages and uses a highly customizable toolkit, allowing for the creation of various malware variants (Figure 5). Through various deceptive tactics, users are redirected to a fake website impersonating reputable services, often those related to banks or government agencies.
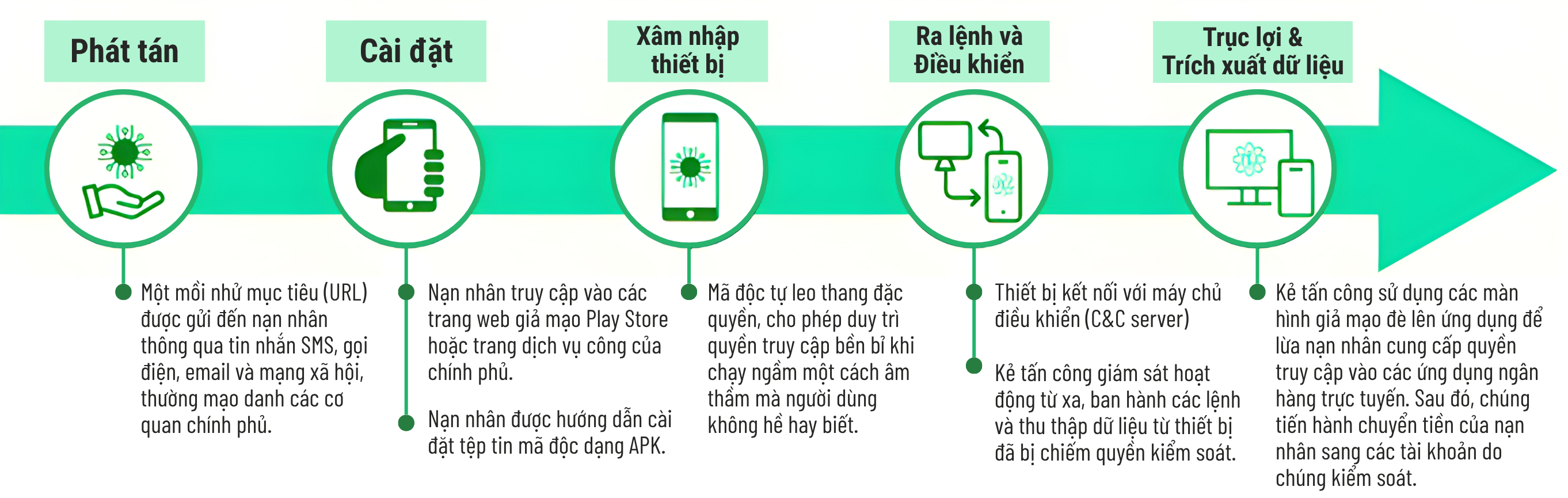
These bait pages prompt users to download a mobile application. The website uses Base64-encoded JavaScript code to distribute a Trojan file as a 23MB APK. When the user clicks the download button, this code downloads the file in chunked segments while displaying a fake progress bar, ultimately leading to the installation of malware on the device.
After the APK file is executed, the application will display a fake login screen, similar to the examples in Figure 6. The actual login interface will vary depending on the specific objectives of each attack campaign.
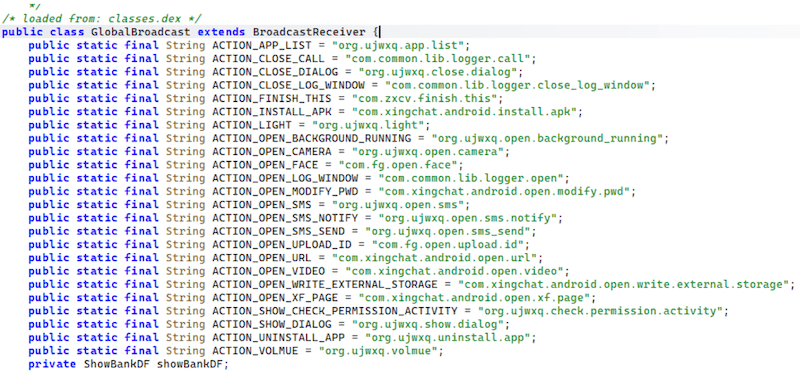
Once installed, the malware operates as a multi-purpose banking Trojan with a wide range of surveillance and intrusion capabilities. As shown in Figure 7, the malware's core functions include: real-time remote control, SMS and call interception, camera and microphone access, credential collection, and the ability to install additional malware. It also contains a comprehensive device fingerprinting module to systematically collect detailed hardware and system information, then compile and send it to the attacker's C2 server.
Inside the malware
Analyzing attack patterns
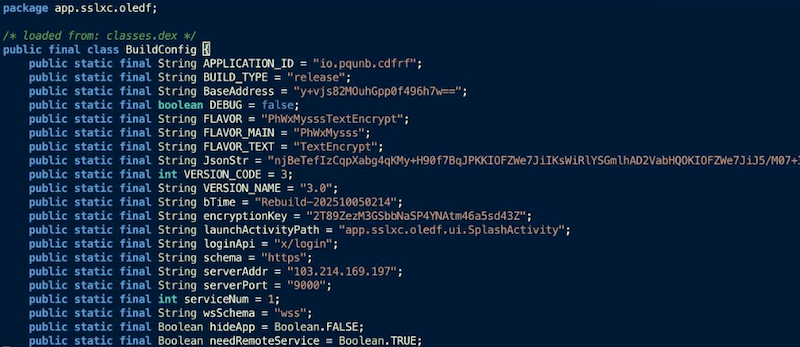
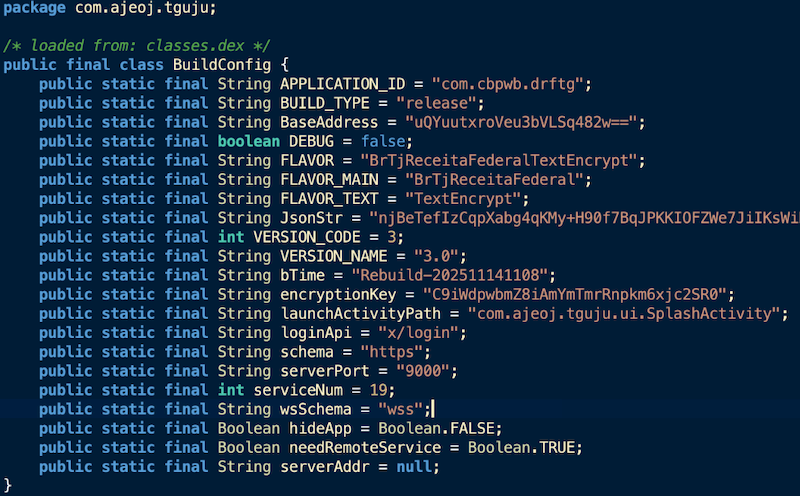
As shown in Figures 8 and 9, upon reviewing the source code, Anti-Phishing experts observed that some early samples included hardcoded information such as IP addresses, ports, login APIs, decryption keys, and other data; whereas later samples used an internal decryption function to dynamically retrieve IP addresses during execution, eliminating any static traces from the source code. This change, combined with updated timelines, BuildConfig, This indicates that the malware is still being actively developed.
Tracing C2 servers
Based on the weak operational security (OPSEC) in older models, it can be inferred that other mistakes would also occur. It didn't take long for Anti-Phishing to find a C2 server exposed due to a lack of proper access control measures. This allowed investigators to monitor the activity of multiple operators, while directly observing the infection process and attacker behavior in real time.
Through access to the exposed infrastructure, experts observed that the operators were deploying customizable permission request dialogs and app overlay screens to deceive victims. Simultaneously, they extracted various data including contacts, notes, photos, SMS messages, and call logs. This data could be immediately used to support further attacks. The operators also used a web-based admin panel to manage multiple infected devices simultaneously, with different workflows depending on the specific victim.
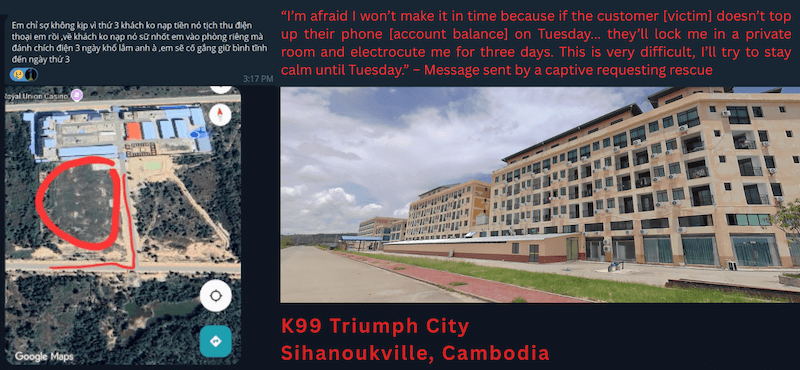
As shown in Figure 10, during the operation, the victim will see an overlay screen requesting digital verification or electronic identification (KYC). Meanwhile, the attacker simultaneously activates biometric data collection in the background. Facial recognition data is then used to log into the victim's online banking application without their knowledge. By intercepting the SMS OTP code from the bank, the operator gains full access to the victim's bank account and can transfer funds wherever they want.
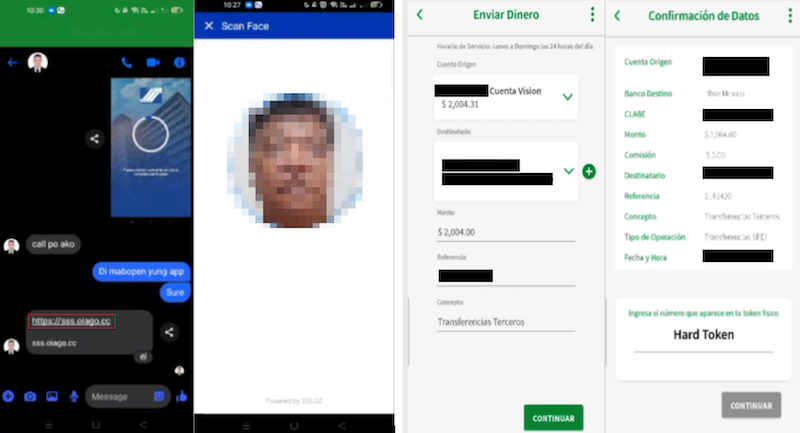
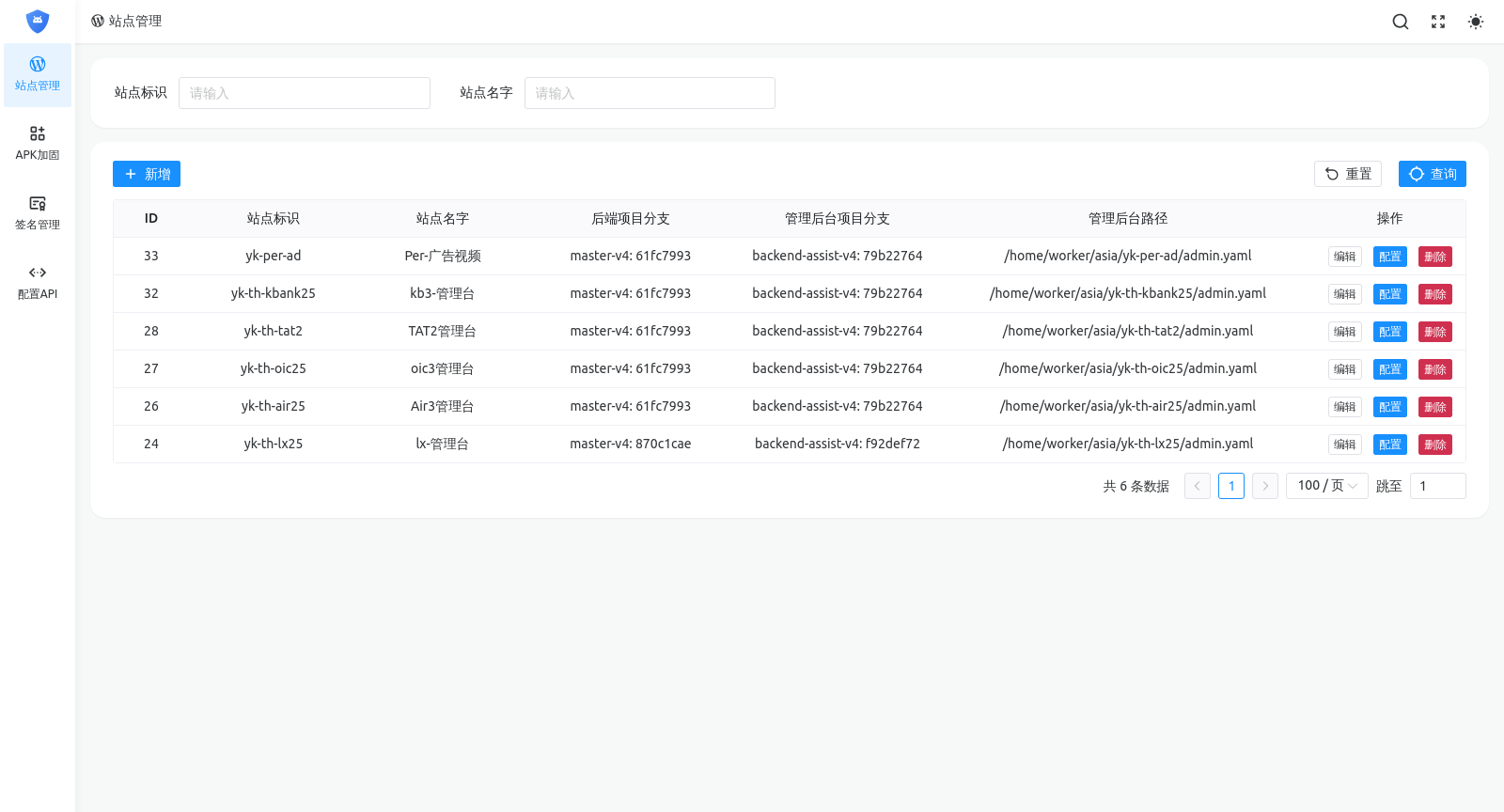
sss.oiago[.]cc via Facebook Messenger; 2) The operator then deploys a fake KYC verification screen; 3) and 4) The operator is withdrawing the victim's funds from BBVA Mexico bank.This MaaS administrator uses specific subdomains, including '‘kef’, ‘ador’, ‘rpc’', as well as '‘admin’' and '‘apim’' for C2 servers and various Android application management panels. The use of regular subdomains helps experts create "identification signatures" to detect additional control servers (C2s). These servers are often set up to serve multiple criminal groups simultaneously. This system includes a series of C2 control panels specifically categorized by target country (such as Indonesia, Brazil, Egypt), or by the individual name of each client renting the service. This demonstrates a highly professional and tightly coordinated operation.
Management infrastructure analysis
Further analysis revealed specialized sub-sectors used to develop modified banking applications and reverse engineering techniques, testing facial recognition and bypassing malware detection mechanisms. They even integrated AI chatbots and deepfake technology into the attack process. Figures 11 and 12 illustrate this point.


Upon closer analysis of the APK management platform of MaaS service administrators (ironically, it resides on the domain name) safeapk[.]xyzAnti-phishing experts have discovered numerous custom applications designed to impersonate organizations in Thailand. As shown in Figure 13, this list includes fake applications impersonating Thai Airways, Kasikorn Bank, LX International, the Office of the Insurance Commission (OIC), and the Tourism Authority of Thailand. These findings are consistent with attack campaigns previously documented through DNS record history.
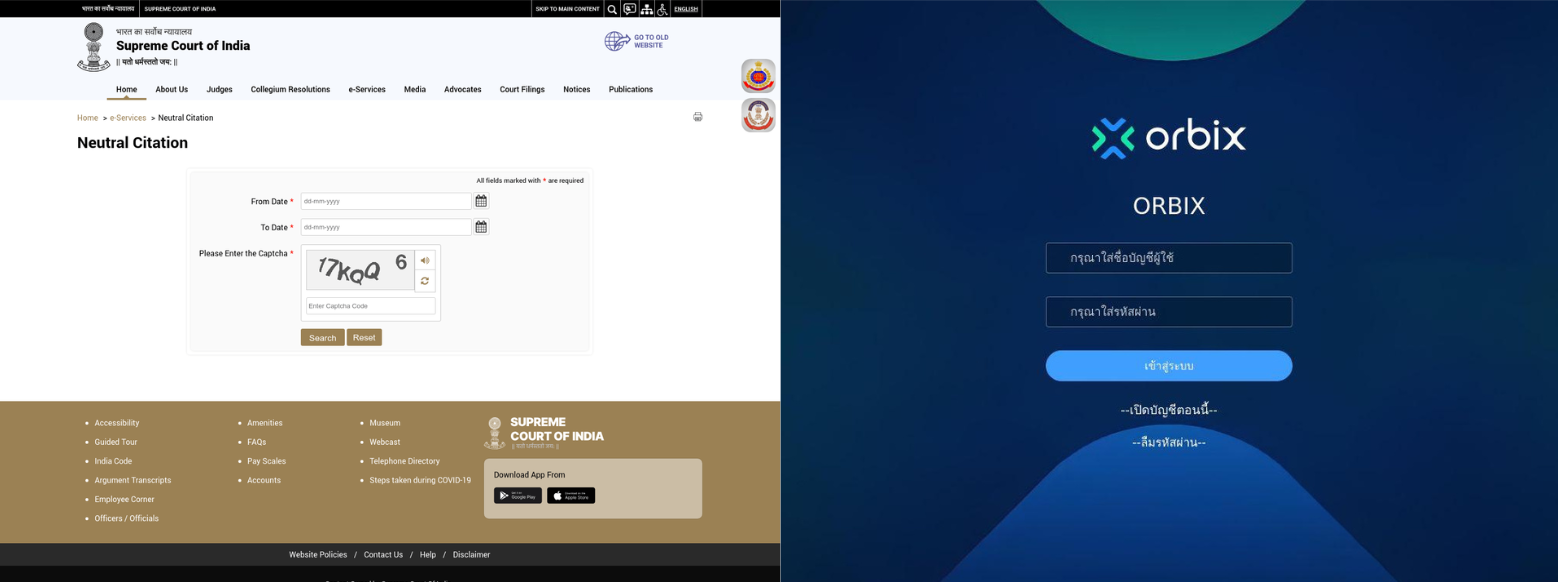
Analysis of the infrastructure and related domains reveals that the same system has been used for various activities, including phishing, cryptocurrency investment scams, and more. pig butchering. They used domain names such as lx-yindu[.]top and orbiixtrade[.]com to impersonate the Supreme Court of India and the Thai cryptocurrency trading platform Orbix (Figure 14), in which the fake Indian Court domain name was reported in an official announcement by the Government of that country.
OPSEC is really difficult (especially when it comes to forced labor).
The victim speaks from inside.
By the end of 2025, some of the detainees had contacted Anti-Phishing to seek rescue from a complex in Sihanoukville, Cambodia – a cybercrime hub linked to the group. Vigorish Viper. These individuals claim they were beaten and tortured with electric shocks for failing to meet performance targets. This accusation is entirely consistent with reports from the United Nations and numerous other organizations that have documented similar incidents in the region in recent years.
After being successfully rescued from the K99 complex, the victims provided the investigation team with crucial evidence: from private group chat logs and screenshots to other relevant data. This material not only reinforced previous findings but also confirmed the existence of malware distribution and phishing as a service (MaaS) operations running on the relevant infrastructure. Notably, the evidence obtained showed that several domains in Infoblox's initial data cluster (Figure 15) were directly used in the phishing campaigns, thus providing a solid basis for concluding that the entire discovery chain is directly related to the K99 location (Figure 16).
Experts examined the work equipment of one of the victims and found targeted victim profiles built on personal data along with detailed business information, as well as pre-written attack scenarios and forged government documents used for social engineering purposes. Notably, a fake government notification related to a new digital identity program and VAT reduction for registered Vietnamese businesses was used to send to the target business owner or employee. Related campaigns also impersonated dozens of other public services, from utility providers to law enforcement agencies.
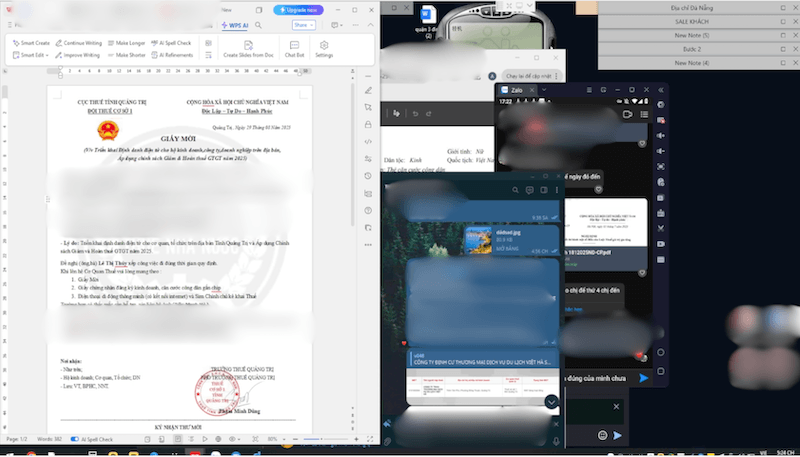
The process of fraud and misappropriation of assets.
According to accounts from those who escaped the scam, the staff would initially contact their targets by phone using software. eyeBeam (a type of internet calling software – VoIP) to impersonate government officials. They then redirect communication to a popular messaging app. Zalo They then send a link or QR code leading the victim to a bait page (as described above). There, they instruct the victim to install a malicious APK file and request advanced access permissions on the device, while telling the victim to ignore any security warnings from the system.
The attacker then closely monitors the infected device before using the collected login credentials to access the victim's banking app. They intercept one-time verification codes (OTPs) sent via SMS to verify identity, and finally manipulate the victim into undergoing biometric authentication (facial recognition) through a professional-looking overlay screen. At this point, the victim is completely convinced that these actions are necessary to comply with a "new government program.".
The harsh reality is that the victim has just completed the final step in giving the scammer full access to their online banking account. The sequence of events is illustrated in Figure 18 below, using images captured from a real-life attack.
The K99 Group and its connection to Vigorish Viper and Vault Viper
According to official business registration records, the complex K99 Triumph City owned by K99 Group (Cambodia). This is a diversified conglomerate operating in the fields of casinos, online gambling, real estate development, and investment. The conglomerate is owned by a tycoon. Rithy Raksmei (also known as Xie Liguang) is the chairman. He is a member of the Senator's family. Kok An – one of Cambodia's richest men, who was once named by the media as a wanted person by Thai authorities for involvement in online fraud and money laundering.
Both individuals were recently named in U.S. House Resolution (HR 5490) alleging they are foreign nationals involved with transnational criminal organizations, maintaining large-scale online fraud operations. Reports also describe them as facilitators of criminal networks operating in Southeast Asia through formal business partnerships, including those led by mob bosses. Alvin Chau (Suncity Group) leads and Dong Lecheng (a person subject to sanctions from the UK and the US), along with many others linked to one of the most notorious scam hubs in Sihanoukville, Cambodia, commonly known as “Chinatown” (Figure 19).
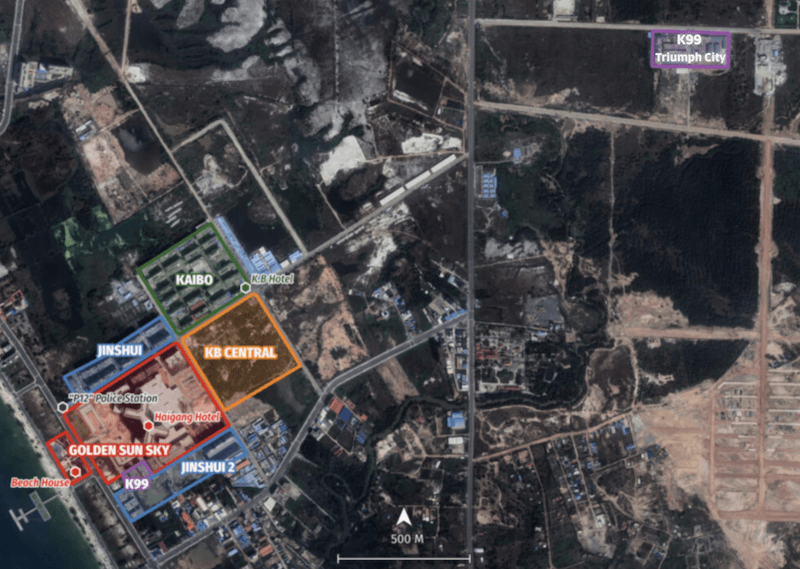
According to a previous report According to Infoblox, “Chinatown” is an isolated area comprising numerous casinos and heavily guarded scam complexes. Since its development began around 2017, it has rapidly become one of the world’s largest high-tech scam hubs. These projects have extensive links to Chinese-speaking criminal networks associated with the names of Kok An and Rithy Raksmei.
The concentration of actors in this area reveals a highly centralized ecosystem where a small group of politically connected “insiders” act as key facilitators, providing access, protection, and maintaining the smooth operation of transnational criminal groups. Individuals involved in these complexes have been documented as having links to regional criminal gangs through large-scale cooperation agreements, overlapping business structures, and shared infrastructure.
Recent reports from human rights groups and other sources indicate that K99 Triumph City remains actively operating despite Cambodian government crackdowns on cybercrime and fraud – a common scenario in large-scale fraud hub networks.
Besides K99's reported links to Senator Kok An, the network has long been described as having close ties to the Cambodian political and military elite (as shown in Figures 20, 21, and 22). Most notably, K99 is located in the same area as the investment company and casino. Royal Union, along with the former director of this company, Yim Leak – the son of Deputy Prime Minister Yim Chhay Ly. Yim Leak is also a name mentioned in the draft Foreign Fraud Gang Dismantling Act of the US Congress. Interestingly, historical records of Leak's involvement in the company have been erased from Cambodia's official business registers in recent months. Fortunately, however, investigators have preserved copies of these records.

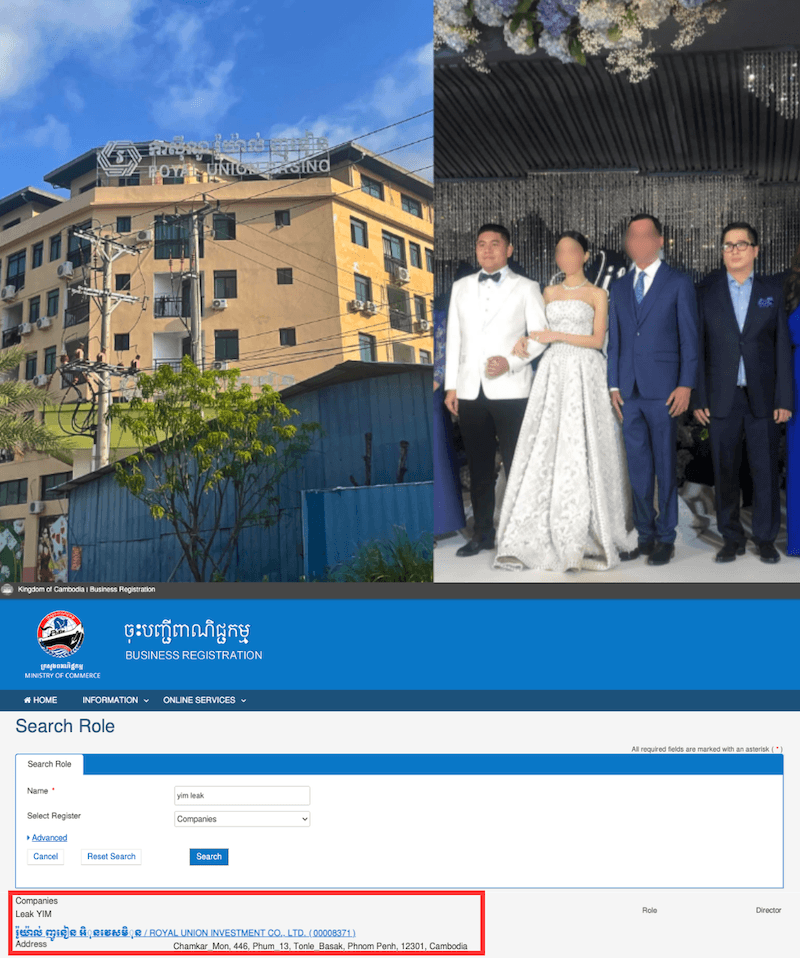

In February 2026, the Anti-Money Laundering Office (AMLO) and the Civil Court of Thailand issued a provisional order. Assets worth 13.07 billion THB (approximately 407 million USD) were confiscated. This relates to Yim Leak, Kok An, and others as part of investigations into transnational high-tech fraud activities.
Persistence and adaptability
This malicious infrastructure remains active and highly resilient. At the time of writing, hundreds of domains are supporting multiple campaigns running simultaneously across three continents. Activities related to this infrastructure are constantly evolving and expanding, sustaining large-scale campaigns targeting countries such as Thailand, Indonesia, the Philippines, and others. Vietnam, while also diversifying its targets to include Africa and Latin America.
Continuous monitoring reveals persistent domain rotation through RDGA algorithms and the registration of new fraudulent domains, demonstrating an unceasing demand from criminal networks in the region. Experts also note the continuous integration of new decoys along with the reuse of old domains for new campaigns.
Figure 23 specifically illustrates this change: a domain name originally used as a decoy to impersonate the Philippine government has been redirected to target customers of a Moroccan bank; or another domain name originally used for investment scams in Thailand has been repurposed to impersonate the Philippine government in order to distribute malicious APK files.
The investigation team's findings reveal the agility and flexibility of criminal groups at fraud centers in quickly deploying readily available tools into practical operation. With abundant multilingual human resources, increasing technical capabilities, and enormous profits, they not only apply but also customize and commercialize malware, infrastructure, and social engineering attack techniques into flexible and highly scalable attack models.
What exists is a dynamic, experimental, and commercially driven ecosystem where tools are constantly reused, improved, and redeployed to maximize reach and profitability. In this environment, “innovation” is not a barrier but a fundamental standard, enabling these networks to sustain and expand sophisticated multi-market fraud operations at lightning speed.
This article is a collaborative product of Infoblox Threat Intel and Anti-Phishing. All technical analysis and visual evidence are derived from joint research by the two organizations. Original article: Infoblox Blog.