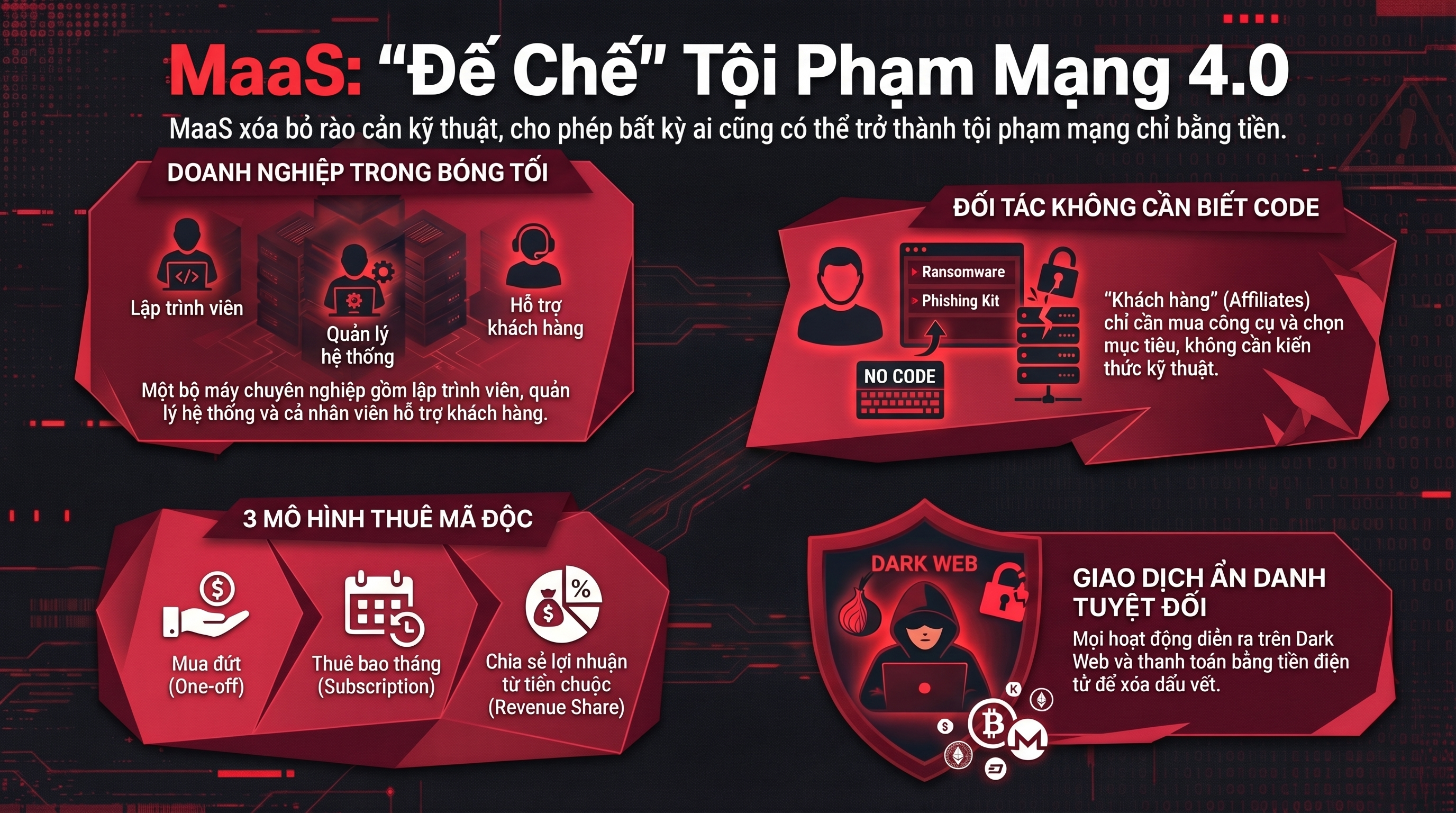
Did you know that today, someone who doesn't know a single line of code can launch a sophisticated cyberattack targeting a multi-million dollar business? No programming skills required. No security knowledge needed. Just… money and a link to the dark web.
That's the terrifying reality that the model Malware-as-a-Service (MaaS) has created, and it is completely changing the face of cybercrime worldwide, including in Vietnam. Anti-Phishing Learn about this model of professional crime.
What is MaaS? In the simplest terms.
If you've ever used Netflix, Spotify, or Google Workspace, you're probably familiar with this model. SaaS (Software-as-a-Service): Pay a monthly fee and use someone else's software without having to build or maintain it yourself.
Malware-as-a-Service (MaaS) It works exactly the same way. But instead of movies or office supplies, what's being "rented" here is... malware (malware) and the entire infrastructure needed to launch a cyberattack.
To be more specific: MaaS is a business model in the underground world where highly skilled hackers develop, package, and rent out cyberattack tools, along with user manuals, 24/7 technical support, and sometimes even a "money-back guarantee if you're not satisfied."“
In the Maas model, the buyer simply pays a fee, receives the tools, and is free to attack any target they want.
MaaS operating model
To understand how MaaS works, imagine it as a software company… but operating entirely in the shadows.
MaaS Operators These are organized hacker groups, usually consisting of:
Affiliates (Partners/Customers) They are the ones who hire the service. They don't need to know how to code; they just need money to buy the "attack kit" and a target in mind.
All transactions took place on dark web, payment by cryptocurrency To conceal their identities, MaaS operators offer a variety of flexible payment options:
Why are MaaS so dangerous?
How can we protect ourselves and our organizations?
With the rise of "malware service" models, users need to be more vigilant:
- Use strong and unique passwords for each account.
- Infostealer will be useless if the password is stolen in one place and cannot be used elsewhere.
- Use a password manager to create and store complex passwords.
- Enable multi-factor authentication (MFA), prioritizing physical security keys or authentication apps.
- SMS OTP is no longer secure enough against AiTM attacks.
- If possible, use a FIDO2/WebAuthn security key or at least an authentication app (Google Authenticator, Microsoft Authenticator).
- Be wary of strange emails and messages.
- Phishing remains the leading intrusion method for MaaS.
- Do not click on links from unknown sources.
- Double-check the sender's email address.
- If in doubt, go directly to the official website instead of clicking a link.
- Update your software regularly.
- Many types of malware exploit vulnerabilities in outdated software.
- Update your operating system, browser, and applications as soon as security patches are available.
- Back up important data.
- Regularly back up your data to an external hard drive (not connected to the network) or a cloud service.
- This is the most effective "insurance" if you are attacked by ransomware.
- Implement comprehensive cybersecurity solutions.
- For businesses, effective protection against MaaS requires multiple layers of defense, including: Antivirus/Anti-malware, Endpoint Detection and Response (EDR), Firewall, Intrusion Detection/Prevention System (IDS/IPS), SIEM, etc.
And most importantly, humans remain the weakest link in the system. Therefore, each individual needs to be supported. Raising awareness about information security This allows us to detect phishing and social engineering before malware can infiltrate our systems.